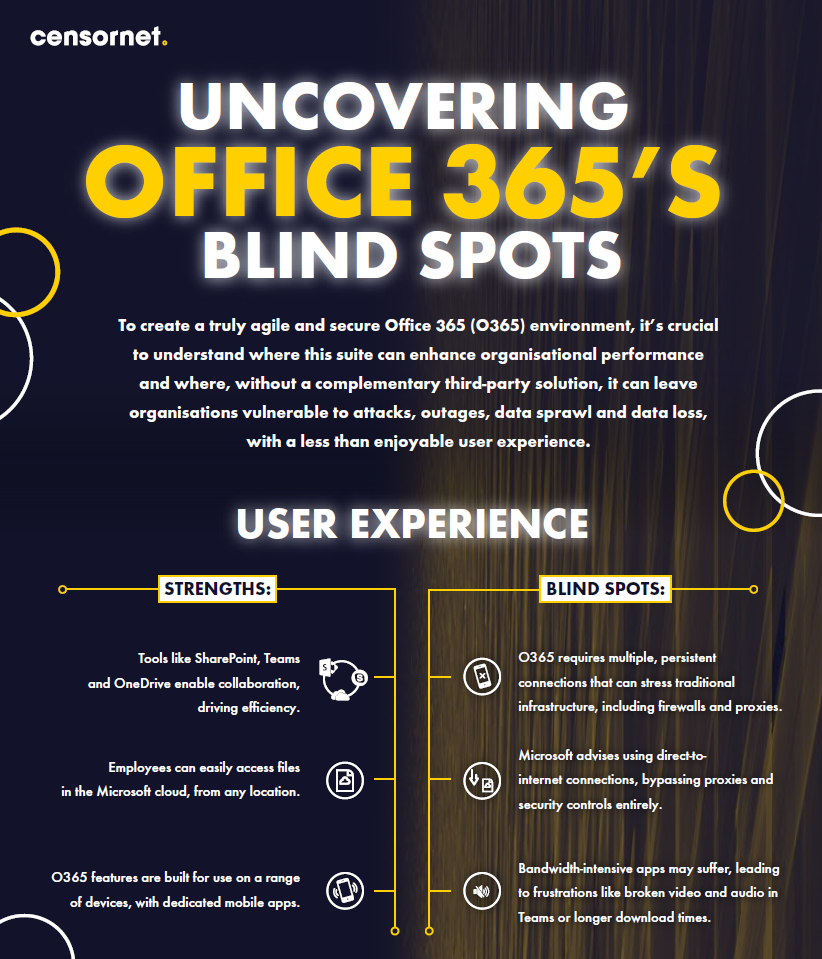
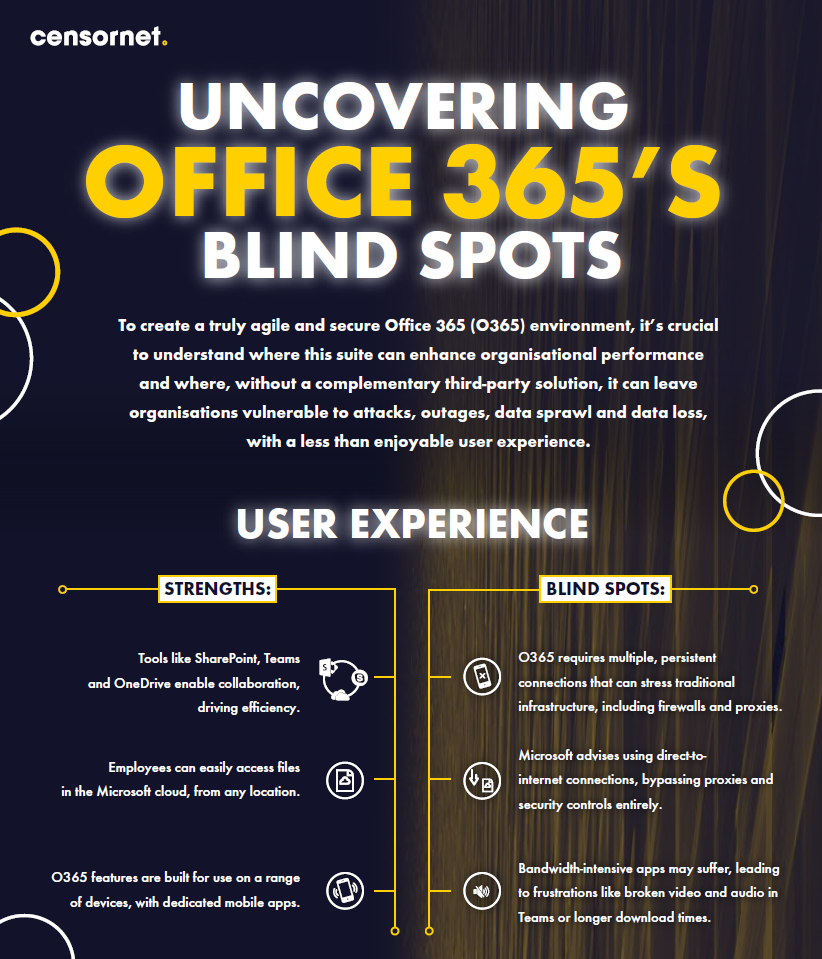
Our infographic offers 20/20 vision into 0365 Blind Spots
This simple infographic outlines the strengths and potential blindspots in key areas.
Download the InfographicGartner infographic.
Critical cyber security challenges.
How XDR is changing the game.
The insider threat that caused the security vs usability conundrum.
How a consolidated approach works.
Key insights and recommendations from Gartner.
Find out in this recorded webinar
The what, why and how of SASE
5 steps for defence
What they are and how to get them right
and how to overcome them
"The biggest cyber threat facing the UK"
The perimeter is no longer “entombed in a box”
Freedom. Visibility. Protection.
with this all-in-one solution
The state of the UK’s cyber security response
View white paper
Zero Trust and Beyond
How to protect your users with email security
Easing alert fatigue
Protect your data in the cloud
Things to consider
And the heightened insider threat
Threatening your business?
9-5 attention no longer cuts it
If it's left behind the cybersecurity curve
Protect your data in the cloud
Share this story
We're a community where IT security buyers can engage on their own terms.
We help you to better understand the security challenges associated with digital business and how to address them, so your company remains safe and secure.