When managing sensitive business projects - whether it involves confidential client data, proprietary technology, or strategic initiatives - the entire team's integrity is crucial.
Yet integrity is only part of the story as personality traits must also be factored in.
The saying "a chain is only as strong as its weakest link" rings particularly true in such circumstances. The weakest link isn't necessarily the most junior or inexperienced team member; it can be anyone whose actions, attitudes, or vulnerabilities compromise the confidentiality, security, or success of projects.
So how do you spot the weakest link in a team working on your sensitive projects and what can you do about it?
Privacy isn't a guessing game - it's about control
It’s almost impossible to know what motivates people at any given time - whether their actions are intentional, or not. In a team working on sensitive business projects, the weakest link might not be who you expect; it could be the most experienced team member, the most social, or even the most disengaged.
Human behaviour is unpredictable, and even well-meaning individuals can inadvertently compromise confidentiality. The only way to ensure sensitive information remains protected is by communicating within a contained environment where privacy is built into the process.
Find out more
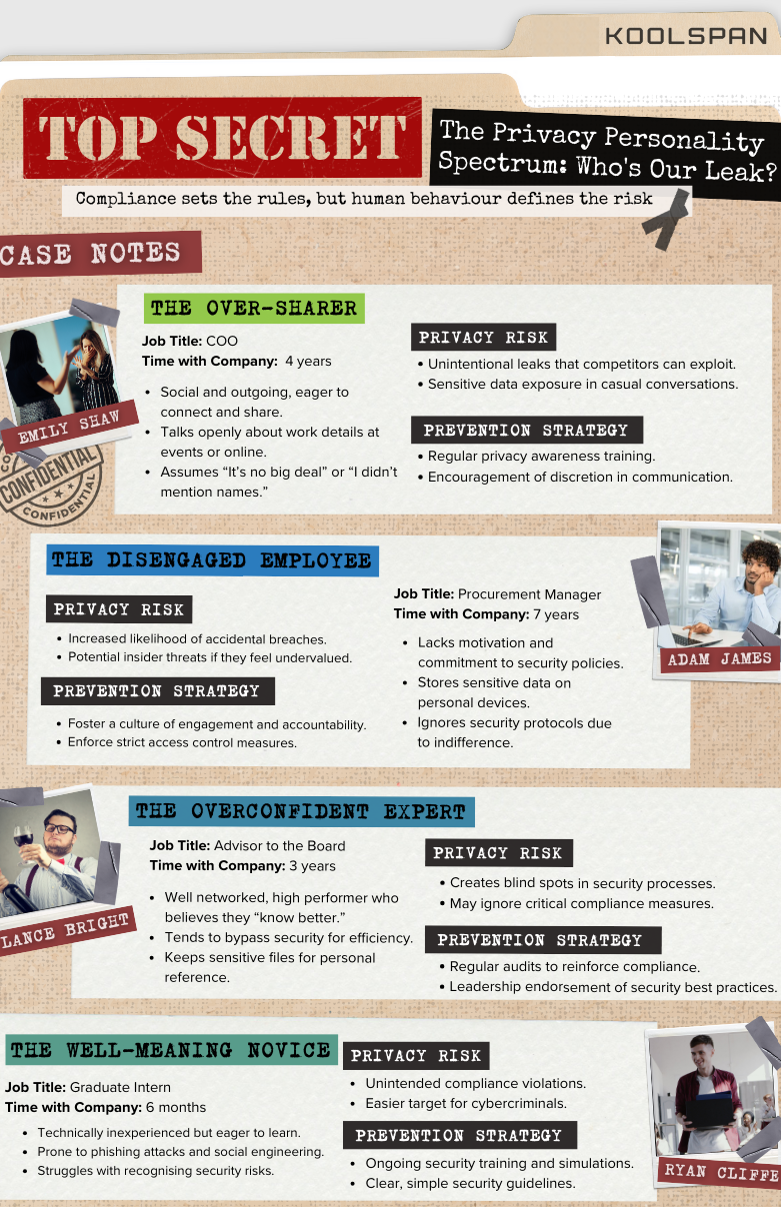
Compliance sets the rules, but human behaviour defines the risk!
Find out more about the privacy personality spectrum from 'the oversharer' to the 'disgruntled employee' - and uncover who is your leak!
Our infographic shows you why privacy isn't just an IT concern - it's a human challenge.
More in KoolSpan
What it means to truly control access.
Why highly secret situations need more than standard cybersecurity.
Why People-Driven Mistakes Are a Serious Matter
Securing data beyond the basics.
Some of the biggest threats to your organisation’s sensitive data come from within.
Threats don't just come from the outside.
Protect your data in KoolSpan Trust Circles
How unsecured communication can derail reputations and market stability
Who's our leak?
Why privacy should be everyone's concern.
Share this story