There’s been a conversation bubbling under the surface of the cybersecurity industry as of late: the merging of security and fraud to break down silos that have given cybercriminals an advantage.
The idea comes from the fact that these two functions are traditionally siloed at organizations, with the security team looking to protect pre-login attacks like account takeover and the fraud team looking to protect the post-login fraud like stealing sensitive information to further other cybercrimes.
But one can’t exist without the other. With fraudsters leveraging sophisticated automated attacks (usually led by bots), the lack of communication between these two teams gives fraudsters the advantage. It goes beyond bots. It’s consequences. In this conversation, panelists from Human discuss and debate the topic.
They cover:
- How companies are approaching current and evolving threats to their customers
- Why the consequences of fraud impacts security teams and vice versa
- Cyber fraud vs cybersecurity: passing trend or the future?
More in Cyber Security
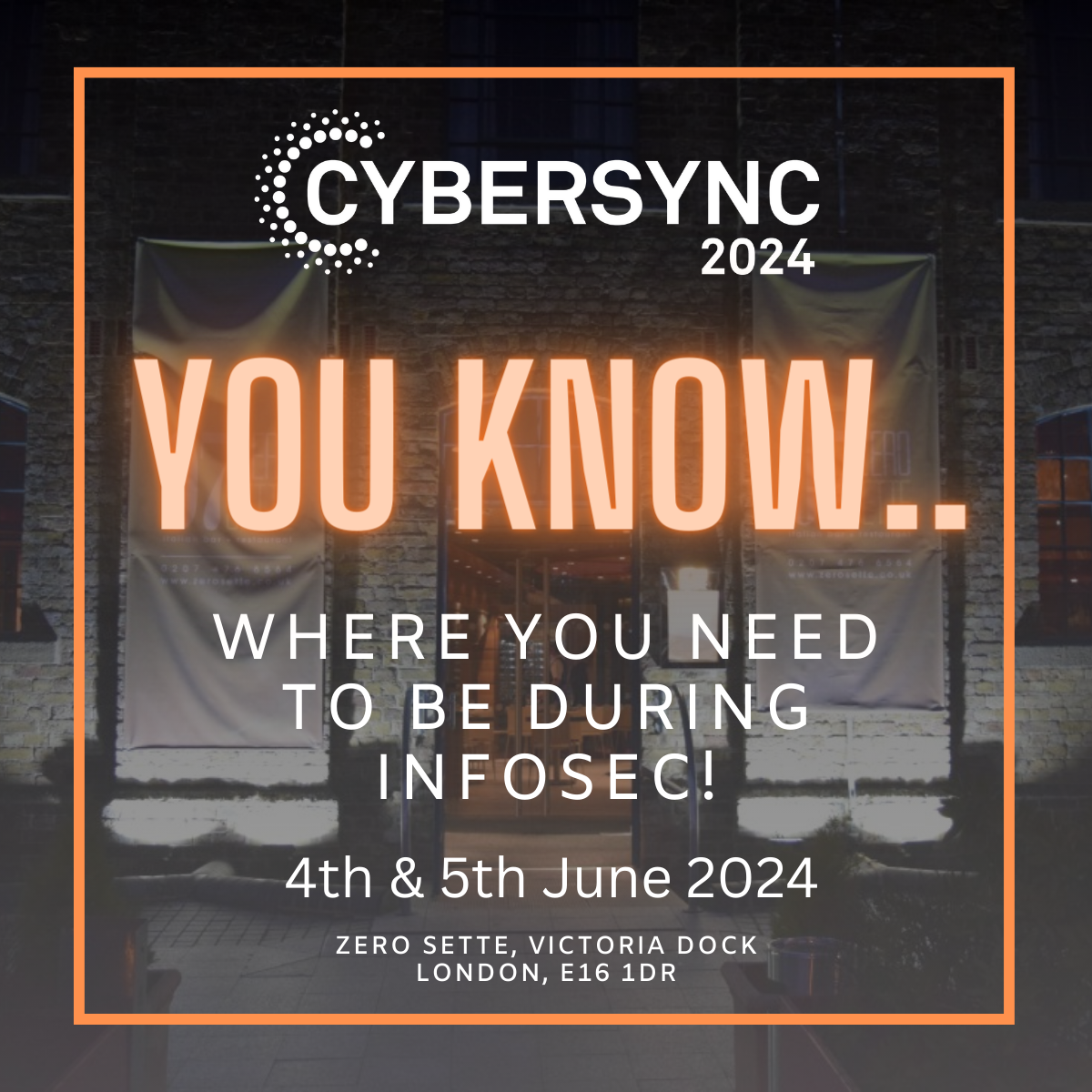
In-person networking and hospitality events for cybersecurity professionals and technology providers.
Security, Safety, and Trust for the AI Era.
Delivering Exceptional Experiences with a Differentiated Portfolio.
AppSec for agentic development.
Cyber resilience that keeps your business in business.
Your AI Isn’t Waiting.
AI-Native. Human-Led. United Against Every Threat.
The AI-Native Social Engineering Defense Platform.
Executive Assurance for Organisational Intelligence and Resilience.
The answer to your biggest data challenges.
Adversary trends and defender strategies derived from real-world telemetry.
Is there a clear line between manipulation and influence, and should security leaders care?
Share this story