Share this story
Read Time: 5 minutes
A recent study of ICO data found that 90% of all security breaches resulted from the actions of employees or other authorised network users.
The study was based on data from 2018-2019, a period well before Covid 19 and the enforced move to remote working. It reflects a time when the majority of employees sat within security perimeters, so how will these statistics change now that we’ve turned our networks inside out?
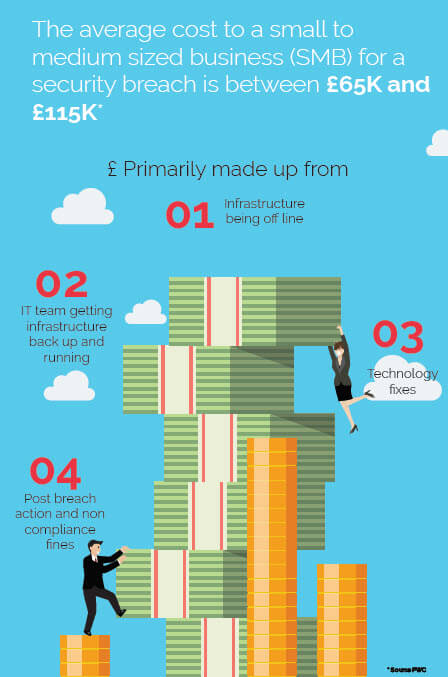
Our focus is on SMBs, who are less likely to have the necessary level of security infrastructure, or the level of investment needed to activate all the policies and procedures required to stop risks caused by the actions of employees, intentionally or otherwise.
Before Covid 19, both the UK and US governments issued a warning about the risks associated with VPN’s, which for most SMBs is an essential tool for enabling remote working. The advice was to implement greater visibility and control over network users and data. With our workforce now flung far and wide, that guidance has a new sense of urgency.
For context, a survey by Kaspersky Lab found that over half of all businesses believed their greatest risk was likely to result from the actions of employees, with the research finding that the biggest worry was the sharing of inappropriate data on mobile, portable and BYOD devices. The loss of mobile devices came second, with inappropriate use of IT resource completing their list of top risks. Now, with the move to remote working, these risks have increased significantly, as businesses are forced to balance operational necessity with their security and well-being.
3 TYPES OF INSIDER THREAT

Accidental breaches are commonplace, with employees inadvertently clicking on malicious links or accessing rogue data in error. Generally, these users will adhere to policies and follow guidance, but carelessness leads to breaches. With remote working placing users outside an office environment, without the full array of support tools and working structures, this is only likely to become a growing risk.

Simple negligence is still the most common form of insider threat. While most employees aim to follow guidelines and policies, a small number don’t - with devastating results. Offenders may not intend to put a business at risk, but don’t buy into the need for policies and practices or find them constraining and obstructive. Whatever the reason, the results the same.
There are many reasons for users to act maliciously, including dissatisfaction, frustration and criminal intent. Again, remote working increases risk in this area, with the danger of ‘insiders’ turning into ‘outsiders’.
Training and awareness are an obvious step to reduce employee-initiated risk but, with remote working, it just got harder.
With businesses forced to work in new ways and across multiple locations and devices, we’ve looked at the steps you can take to reduce your risk.
- Establish a set of ‘workable' security policies
It’s essential to have a set of basic and workable policies for network use that provide a minimum level of security over the assets passing through the network and the people who use it.
By establishing this base point, it’s possible to identify anomalies in personal usage and behaviour and take steps to stop them, whether they’re intentional or accidental - cyber criminals don’t care.
There are technologies now that can do this easily and without the need for additional hardware or complex IT intervention.
Many now use AI to learn from network activity and establish behavioural patterns to enhance policies, improve performance and reduce risk. For SMBs, these technologies are ideal, providing the visibility and control recommended by government security experts. - Take steps to prioritise risk
With nearly 60% of all businesses accepting they will at some point experience a breach of their networks, risk assessment is a critical aspect for any IT security team, best illustrated by the increasing number of high profile breaches of big businesses with deep pockets.
SMBs more than most need to prioritise workload and address the greatest risks first. With remote working, keeping track of users must be at the top of priority list. Technologies that track anomalies will allow you to prioritise actions to stop accidental or malicious activity.
Unrecognisable devices or locations, accessing unusual assets and other behavioural patterns can be monitored and alerts issued, with some technologies blocking actions before breaches can occur. Again, AI will help ensure policies reflect changing business trends. - Get visibility over your network
None of the above can be achieved without full visibility of your network and the people who use it, which is why visibility is one of the 2 key points of guidance from both the UK and US cyber security agencies.
Without visibility, you can’t apply the second, which is control - you can’t stop what you can’t see. With remote working turning networks inside out, the need to understand what’s happening on your network is one of the most critical aspects of any security policy, helping to monitor how users work and what they access.
Visibility won’t stop employee-initiated breaches, but it will go a long way towards it. There are now cloud based products that specifically address the monitoring of network traffic to provide visibility and control of users and assets.
Many of these products can be introduced without disrupting existing IT systems and requiring little maintenance or resource, essential factors for SMBs when selecting a manageable solution.
According to Gary Hudson, publisher of Human Error, a website set up solely to address employee-initiated risk, there has never been a more critical time to take action to stop human error. “If the problem wasn’t bad enough when our networks were within our security layers, we’ve now turned everything inside out. Our users are no longer behind well maintained defences but are spread all over the place. The margin for and risk from human error has grown exponentially.”
"If ever there was a need to rethink your security strategy, now’s the time."
Gary Hudson, Publisher of Human Error
Hudson believes the IT sector must wake up to the biggest cause of security breaches. “If ever there was a need to rethink your security strategy, now’s the time. Remote working has opened our networks up. We’re seeing a proliferation of new devices, many BYOD, to enable remote working. We’re less in control of our users and those users are in their own worlds with their own set of rules. There’s too much at stake to let that continue”.

This article was sponsored by CyGlass, an advanced threat detection product that offers visibility and control over network traffic.
Features that include dark threat detection, critical asset protection and compliance for small financial institutions, specifically target insider threats by detecting malicious activity and human error. CyGlass is affordable, can be implemented in minutes and is currently available for 90 days at no cost.
Let us know what you think about the article.