In Association With MYREDFORT
4 steps to safer emails
Share this story
Read Time: 3 minutes
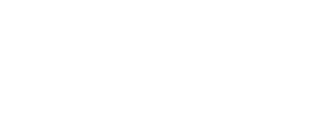
Scary, isn’t it? But what isn’t always recognised is the inability of some of the leading workplace technologies to provide the necessary level of protection.
In recent weeks, we’ve spoken of the vulnerabilities of VPNs and workplace technologies, with visibility and control an important issue, yet email is such a big area of risk that we decided it needed particular attention.
Shaun McKay, our guest consulting CIO, gave us his view. “Microsoft 365 just doesn’t have sufficient protection from email attacks, but many people don’t realise it and, with more businesses fast tracking digital transformation programmes as a result of the pandemic, Microsoft 365 is fast becoming the most adopted business productivity suite.
“While there’s no doubt about its value and power for automating business, email is one area where there’s a clear need for additional security. I use a simple self-serve tool for testing email security on Microsoft 365 and, in almost all cases, users are shocked when they see the results”.
1. Microsoft 365 Protection:
Don’t rely on Microsoft 365 alone – enhance your Microsoft 365 email security for best possible protection.
Read more about the risks of Microsoft 365 here. If you’d like advice on how to enhance Microsoft 365, click here and we’ll put you in touch with people who can help (we won’t give your details to anyone - we’ll give you a selection to choose from).
2. Email Security Test:
Know how secure you email is by testing the security of your email system. We have a simple test you can do that’s been recommended by top UK law enforcement agencies – just click here.
3. Advanced Email Security:
Use an Advanced Email Security product that includes, at the very least, the following features:
4. Email Security Policy:
Remember, most security breaches come for the actions of employees or other authorised network users (see our sponsored post, "The Threat From Within"). Education is essential, so communicate details of your email and cyber security policies to all users and provide them with access to improved security features.
Last week, we reported that global cyber-crime was predicted to reach $5 trillion next year, increasing from $3 trillion and with no allowance for Covid 19. “It’s not just about cost” says Shaun, “cyber-crime is a serious threat to a business’s reputation as well. Now more than ever, having the right protection is essential”.
ASL has been providing IT Security software and hardware solutions that we integrate into our customer's platforms for over 20 years. When you choose ASL you get more than just a supplier, you gain a partner who will always deliver.
Our email security partner, Libraesva, was awarded not one, but two of the top awards at the Computing Security Awards in December 2021, winning both the best email security category and the best email phishing solution.
Computing recognised that Libraesva was best in class against all the top email security providers, which is probably why they are one of the fastest growing email security solutions worldwide.
Working with our skilled engineers who have extensive experience of computer technology for most business sectors, you can depend on ASL to deliver the most up to date and reliable solutions for your applications - on time, within budget and exceeding your expectations.
Together, ASL and Libraesva are a good fit whatever you do, with top customers in any number of sectors.
Phishing is a form of fraud in which an attacker masquerades as a reputable entity or person in email or other forms of communication. Attackers will commonly use phishing emails to distribute malicious links or attachments that can perform a variety of functions. Some will extract login credentials or account information from victims.

Most phishing attacks are sent by email, where a fake domain is registered that mimics a genuine organisation. The fake domain often involves character substitution, like using ‘r’ and ‘n’ next to each other to create ‘rn’ instead of ‘m’.
Alternatively, they might use the organisation’s name in the local part of the email address (such as paypal@domainregistrar.com) in the hopes that the sender’s name will simply appear as ‘PayPal’ in the recipient’s inbox.
There are many ways to spot a phishing email, but as a general rule, you should always check the email address of a message that asks you to click a link or download a attachment.
Spear phishing, describes malicious emails sent to a specific person. Criminals who do this will already have some or all of the following information about the victim:
Whaling attacks are even more targeted, taking aim at senior executives. Although the end goal of whaling is the same as any other kind of CEO Fraud - CEO fraud, is when attackers abuse the compromised email account of a CEO or other high-ranking executive to authorise fraudulent transfer of funds to a financial institution of their choice.

With both smishing and vishing, telephones replace emails as the method of communication. Smishing involves criminals sending text messages (the content of which is much the same as with email phishing), and vishing involves a telephone conversation.

A relatively new attack vector, social media offers a number of ways for criminals to trick people. Fake URLs; cloned websites, posts, and tweets; and instant messaging (which is essentially the same as smishing) can all be used to persuade people to divulge sensitive information or download malware.

As users become wiser to traditional phishing scams, some fraudsters are abandoning the idea of “baiting” their victims entirely. Instead, they are resorting to pharming.
This method of phishing leverages cache poisoning against the domain name system (DNS). Under a DNS cache poisoning attack, a pharmer targets a DNS server and changes the IP address associated with an alphabetical website name. That means an attacker can redirect users to a malicious website of their choice. That’s the case even if the victim enters the correct site name.
We're a community where IT security buyers can engage on their own terms.
We help you to better understand the security challenges associated with digital business and how to address them, so your company remains safe and secure.
The dangers of complacency
(in fact, pretty much don’t auto-renew anything in life!)
Things to consider when an email security vendor is acquired by a bigger beast
myredfort looks at email security for all with Libraesva
Email Security: Removing the guesswork
Email Security for all with LibraESVA
Libraesva email security solution wins top 2 awards
Email Security, Archiving & Encryption