Please get in touch if you need any advice and we’ll connect you with an expert who can help (we won’t give your details to anyone - we’ll give you a selection to choose from).

Please get in touch if you need any advice and we’ll connect you with an expert who can help (we won’t give your details to anyone - we’ll give you a selection to choose from).

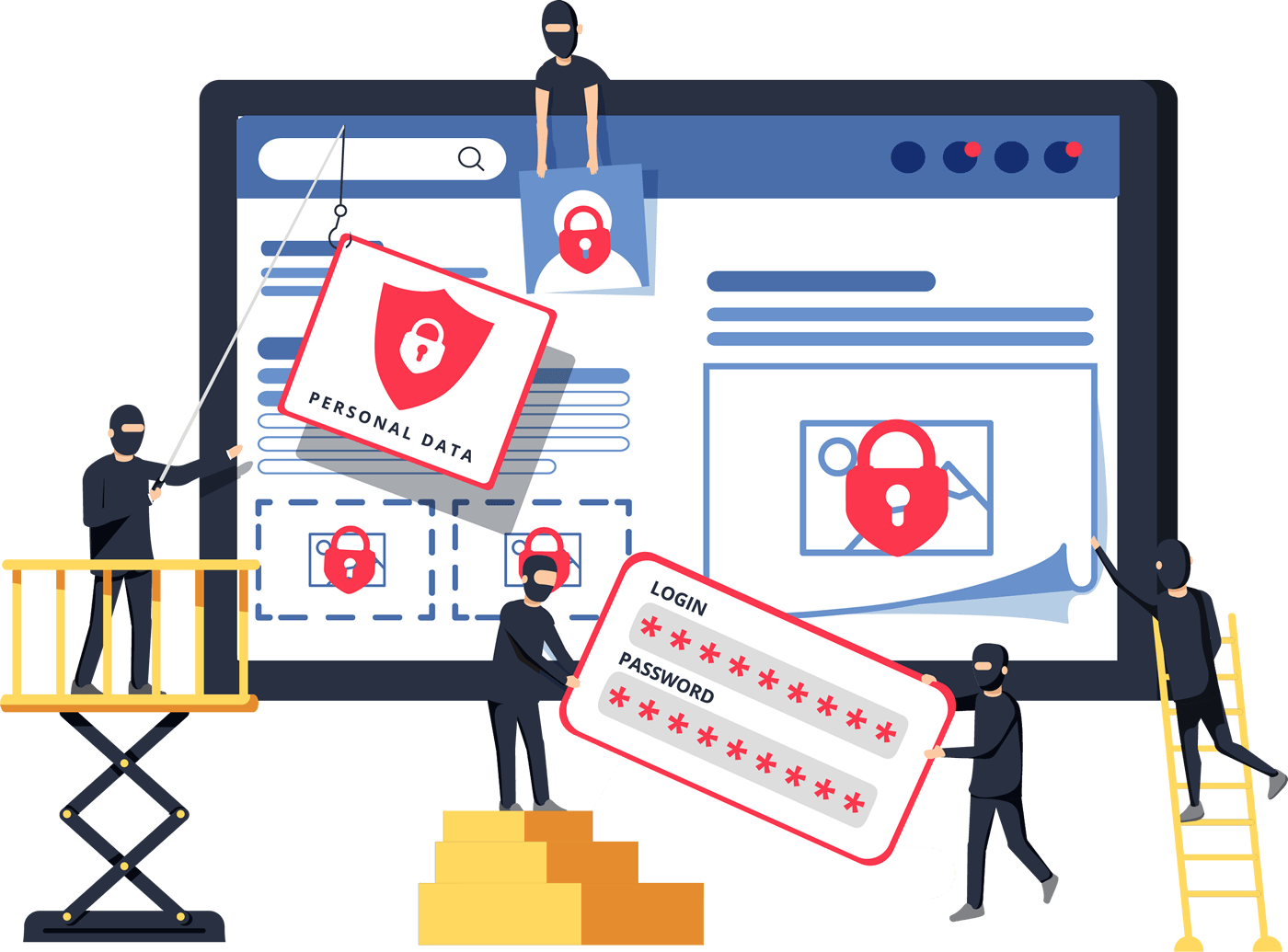
There are four types of hackers:

These are adolescents who are essentially Internet vandals and are also known as Script Kiddies.
They use existing computer scripts or codes to hack into computers because they lack the expertise to write their own. They're not looking for more than a few hours of fun messing with websites or networks, but have the ability to cause havoc.
These are savvy computer users who intrude on networks when they feel, in their minds at least, they have a valid reason to.
They may have a grudge against a certain website or company and take their dislike out by "hacking" or disrupting the website. Or they simply want to use their skills to make easy money.
When a computer expert or recreational hacker gets a taste for hacking or enjoys the buzz, he or she will continue to use their skill, often to steal money, or cause maximum disruption and reputational damage.
They use deception to obtain personal information that they will use for many purposes, not least to or demand ransom payments or to trick account owners into handing over bank details. They also might like taking down a big network for "fun."
Ethical hacking (or penetration testing) is the exploitation of an IT system with the permission of its owner to determine its vulnerabilities and weak points.
It’s an effective way of testing and validating an organisation’s cybersecurity vulnerabilities, check incident detection and response process.
Hackers can be individuals, or part of a team of people employed to find and use personal details for the purpose of building individual profiles to target them for fraudulent purposes. Phishing is big business and can range from small time scams to organisational extortion.
Whether it’s ego or money driven, the effects can be devastating costing businesses £tens of thousands in downtime, reputational damage and non-compliance fines.
Just think about it. If your HR database is breached, your business could be responsible for any impact or loss sustained by one of your employees.
Who Can Be Targeted?
Most people associate phishing with e-mail messages that spoof, or mimic, banks, credit card companies or other business like Amazon and eBay.
However, they can be made to look like they come from someone a business trades with regularly – or even someone internal to the business such as the CEO or HR department.
These messages look authentic and attempt to get victims to reveal their personal information. But e-mail messages are only one small piece of a phishing scam.
What happens in a Phishing attack?Phishers decide which business to target and determine how to get e-mail addresses for the customers of that business. They often use the same mass-mailing and address collection techniques as spammers.
Once they know which business to spoof and who their victims are, phishers create methods for delivering the message and collecting the data. Most often, this involves e-mail addresses and a Web page.
This is the step people are most familiar with -- the phisher sends a phony message that appears to be from a reputable source.
Phishers record the information victims enter into Web pages or popup windows.
The phishers use the information they've gathered to make illegal purchases or otherwise commit fraud. As many 25% of the victims never fully recover
If the phisher wants to co-ordinate another attack, he evaluates the successes and failures of the completed scam and begins the cycle again.
Phishing scams take advantages of software and security weaknesses on both the client and server sides. But even the most high-tech phishing scams work like old-fashioned con jobs, in which a hustler convinces his mark that he is reliable and trustworthy.
Banks are putting more safeguards in place, but aren’t obliged to refund the stolen cash as they are with unauthorised or fraudulent payments on credit and debit cards.
Despite victims being tricked into transferring funds, banks will say the payments were "authorised" and they simply followed the payee's instructions.
Under GDPR compliance rules, businesses face hefty fines if personal data is stolen therefore needs to put safeguards in place.
Improve Your Cyber SecurityPhishing is a form of fraud in which an attacker masquerades as a reputable entity or person in email or other forms of communication. Attackers will commonly use phishing emails to distribute malicious links or attachments that can perform a variety of functions. Some will extract login credentials or account information from victims.

Most phishing attacks are sent by email, where a fake domain is registered that mimics a genuine organisation. The fake domain often involves character substitution, like using ‘r’ and ‘n’ next to each other to create ‘rn’ instead of ‘m’.
Alternatively, they might use the organisation’s name in the local part of the email address (such as paypal@domainregistrar.com) in the hopes that the sender’s name will simply appear as ‘PayPal’ in the recipient’s inbox.
There are many ways to spot a phishing email, but as a general rule, you should always check the email address of a message that asks you to click a link or download a attachment.
Spear phishing, describes malicious emails sent to a specific person. Criminals who do this will already have some or all of the following information about the victim:
Whaling attacks are even more targeted, taking aim at senior executives. Although the end goal of whaling is the same as any other kind of CEO Fraud - CEO fraud, is when attackers abuse the compromised email account of a CEO or other high-ranking executive to authorise fraudulent transfer of funds to a financial institution of their choice.

With both smishing and vishing, telephones replace emails as the method of communication. Smishing involves criminals sending text messages (the content of which is much the same as with email phishing), and vishing involves a telephone conversation.

A relatively new attack vector, social media offers a number of ways for criminals to trick people. Fake URLs; cloned websites, posts, and tweets; and instant messaging (which is essentially the same as smishing) can all be used to persuade people to divulge sensitive information or download malware.

As users become wiser to traditional phishing scams, some fraudsters are abandoning the idea of “baiting” their victims entirely. Instead, they are resorting to pharming.
This method of phishing leverages cache poisoning against the domain name system (DNS). Under a DNS cache poisoning attack, a pharmer targets a DNS server and changes the IP address associated with an alphabetical website name. That means an attacker can redirect users to a malicious website of their choice. That’s the case even if the victim enters the correct site name.
And getting your business through it: Cyber Security Edition
When Office 365 isn't secure enough
You can’t protect what you can’t see
Alarm bells should be ringing with cyber security teams following recent guidance issued by both UK and US government security experts.
Before Covid 19, many SMB’s and mid sized enterprises were embarking on a journey to workplace automation and a world of greater performance, flexibility and control
With more employees now working from home, the risk of breaches has grown exponentially.
Some think that hackers are "cool" and that their spirit of mischief and sneaking is admirable.
50% of IT leaders don’t know if their cyber security is working
Any business feels the pain
Libraesva is an award winning email management tool that works seamlessly with Microsoft 365 to protect all your business emails with zero impact on email performance. To address these failings, Libraesva has additional features that work with Microsoft 365 to provide greater security
Now there’s a simple ‘plug and play’ solution that takes out the complexity and resource needed to provide the SMB IT team with all the information it needs to take action on imposing threats.
Blackberry Desktop is an alternative to traditional VPN’s, offering secure email, calendar and the ability to edit and share documents with absolute confidence. A world leader in cybersecurity, Blackberry Desktop is available at a fraction of the price of traditional VPN’s and is free to use for 60 days.